IT Security
Infostealers reveal everything: your logins, identity, and even your home address.
Talk: Microsoft Entra ID – Defense
Our recommendations for setting up the Entra ID tenant, conditional access policies, what to monitor, and with which tools to audit Entra ID.
Talk: Microsoft Entra ID – Lateral Movement & PersistenceTalk:
After a successful phishing attempt, attackers aim to elevate their privileges and maintain access to the compromised Entra ID environment for as long as possible.
Talk: Microsoft Entra ID – Attack Surface
Technical training on how attackers gain access to Office 365 / Microsoft Entra ID.
Moving to Azure Active Directory
I want to strengthen the security level of our environment, and I think that AAD can help us with that for the following reasons.
Why I want to deploy EDR to all customers
What is EDR? What does it offer? Why do I think it is great technology for any company dealing with IT security.
Overblown Expectations from Security Technologies
Four frequent and unrealistic expectations from SIEM and sandbox I often encounter.
Cutting Down Trees in Our Forest
Last week, hackers managed to break in and encrypt one server of our customer 😤.
The Myth of Cybersecurity Training for Employees
In other words, why employee training is not what most companies need.
How to start a career in cybersecurity?
Tips for starting a career in cybersecurity. Distilled experiences of my friends and me. Courses, websites, certifications, duration.
How Difficult is to Detect a Data Leak
Data leak? After a hacker attack, companies usually ensure the public that no personal data has been leaked. But, how do they know it?
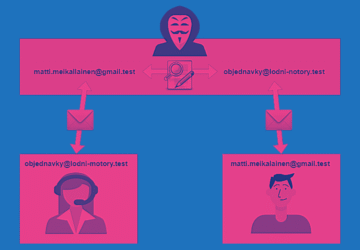
Business E-mail Compromise: Leading Cyberattacks
Business E-mail Compromise cyber attacks type Counterfeiting emails, identity theft aimed at making money. How do the BEC attacks work?
How Could Hackers Attack Vltava Basin? OSINT Research
How to use publicly available information and find a security flaw in the network? OSINT method and Vltava Basin hack case study.
Why Using VPN to Secure RDP Will Not Stop Hackers
Wondering how to increase RDP (remote desktop) security? Let me tell you how hackers most often hack RDPs and why VPN won't change anything about it.
How Hackers Attack Companies Through Their IT Providers
No matter how much you invest in IT security if your provider messes around. Beware of hacker attacks through providers.
Hackers came up with a new trick. They learned to improve their blackmailing with ransomware
Ransomware actors have a new trick. None of backup solutions can mitigate it. They are threatening to release all the stolen information.
What hackers can do in your network
Companies end up without data or backups after a ransomware attack because they underestimate the skills of hackers. Learn what a hacker can do within your network and how to improve security.
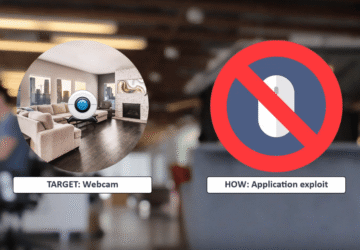
Security insights: Laptop webcam hack
Did you tape your webcam because you're afraid of hackers? The video shows how easy it is to hack a laptop webcam. Do you know how to defend getting hacked?
HackerFest 2019 Workshop Sample
We have made one Linux virtual server available for you to hack from the comfort of your home just after the HackerFest 2019. Go on!
OSCP: Offensive Security Certified Professional
Over 60 servers hacked, 5 months of life and 1 exam. My path to OSCP certification: Offensive Security Certified Professional.