Business E-mail Compromise: Leading Cyberattacks
With “computer crime”, we’ll probably think of ransomware. That’s why you might be surprised reading that cybercriminals make more money on business e-mail compromise (abbreviated as BEC).
What Is a Business Email Compromise?
Although the “business e-mail compromise” may sound new and mysterious, it’s been here for a long time. This includes scams where criminals try to “overwhelm” the victim and get money out of them. These scams often involve the e-mail “forgery” or even identity theft. (If you come up with simpler / more precise definitions, I would be glad if you could share your comment.) 🙂
For example, an unsolicited/unexpected invoice for services that will be sent to a company via e-mail (see 2014 “Fake domain renewal requests are spreading, warns CZ.NIC“[CZ]). Or a fake e-mail in which the director of the company urges the accountant to quickly pay the attached invoice (see 2017 “Beware of fraudulent e-mail. The company in the Zlín region has lost almost half a million crowns“[CZ]).
So why would we open this topic? Criminals have been improving and the current fraud “scenarios” are much more sophisticated and more expensive for the victims. And even though we are “protected” by the Czech language barrier, many companies also communicate in English. And thus Czech companies fall victim as well. At the same time, fraudsters are succeeding in stealing and ever more expanding. We have already been contacted by several Czech companies this year. 🙂 I, therefore, think that we need to raise awareness on this subject to start fighting the fraud.
How Big a BEC Business Is?
According to the FBI´s “2019 Internet Crime Report“, criminals made $ 1.77 billion with the BEC fraud in 2019. As a result, this type of fraud occupies the first place in the rankings with multiple leads over ransomware.

Source: https://pdf.ic3.gov/2019_IC3Report.pdf
You may be wondering why does the ransomware has such a “low” loss. The amount does not include the cost for reintegration and lost business (usually several times the ransom). Yet another reason is that most companies do not report the ransomware attack to IC3 (report source), therefore losses are not included.
To track cybercriminals operating with ransomware and ransom payments I recommend the lecture “Feds Fighting Ransomware: How the FBI Investigates and How You Can Help“.
Global Business Email Compromise
I have selected a few recent successful BEC scams below. Considering that the highest-paid (as far as I know ) ransomware ransom has been $ 2.3 million, the BEC is in a completely different league.
- Norfund (2020) – Norwegian state fund focusing on investment in developing countries lost $10 million. It has sent the funds “voluntarily” (as part of a sophisticated BEC fraud). Interestingly, they came across the scam (allegedly – according to the source) once the criminals tried to get more money from them. („Hackers Steal $ 10M in “Wonderfully Done” fraud from Norway’s State Investment Fund“)
- Tecnimont SpA (2019) – The criminals pretended to be the executives of the entire group and persuaded the management of the Indian subsidiary to make a payment of $ 18.6 million to their account. („Chinese group swindles $ 18.5 million from the Indian arm of Italian company: Economic Times“)
- Toyota Boshoku Corporation (2019) – lost about $37.5 million in a sophisticated BEC fraud. („Over $ 37 Million Lost by Toyota Boshoku Subsidiary in BEC Scam“).
One Practical Experience From The Czech Republic
BEC does not concern only foreign companies. Several companies have turned to us with a similar problem in the last year alone. To outline how sophisticated the scams are, I’ll try to describe one scam we encountered.
You may come up with a lot of “buts” in a given story. But consider that the story is simplified and that the main goal is to illustrate the fraud. In reality, the more money fraud concerns, the more resourceful criminals are. There is usually a more frequent e-mail exchange, theft of multiple identities, and fake phone calls (see “Caller ID spoofing“). Even fake companies can be set up (eg “The Modus Operandi of EV Certificates Fraudsters: Findings from the Field“).
Step #1: Email Account Breach
It all started with the criminals gaining access to the victim’s e-mail account. They achieved this “phishing” or because the victim used the same password for other services and it was leaked (see” credential stuffing“, or how leaked passwords are misused).
Our case will be illustrated by the victim matti.meikalainen@gmail.test. Of course, that’s not the real name of the victim, which will be kept discreet. This is a fictitious e-mail with the Finnish equivalent of the Czech “Jan Novák”. I chose a foreign name deliberately, as there are people of different names in foreign companies. It is then easy for Czechs to overlook the “typo” (see below).
Step #2: Studying the Victim’s Communication
The criminals searched the victim’s mailbox and tracked with whom and what the victim was writing about. They were searching for something that might suit them. For example:
- Whether the victim is making invoice payments.
- Whether the victim issues/send invoices.
- Whether the victim supervises someone who makes corporate payments.
The criminals found out that the victim was running a boat repair shop and wanted to order a new boat engine recently. It was an engine from the “lodni-motory.test” manufacturer for 10,500 €. However, the victim did not place the order. Criminals utilized this information.
Step #3: Fraud Prep
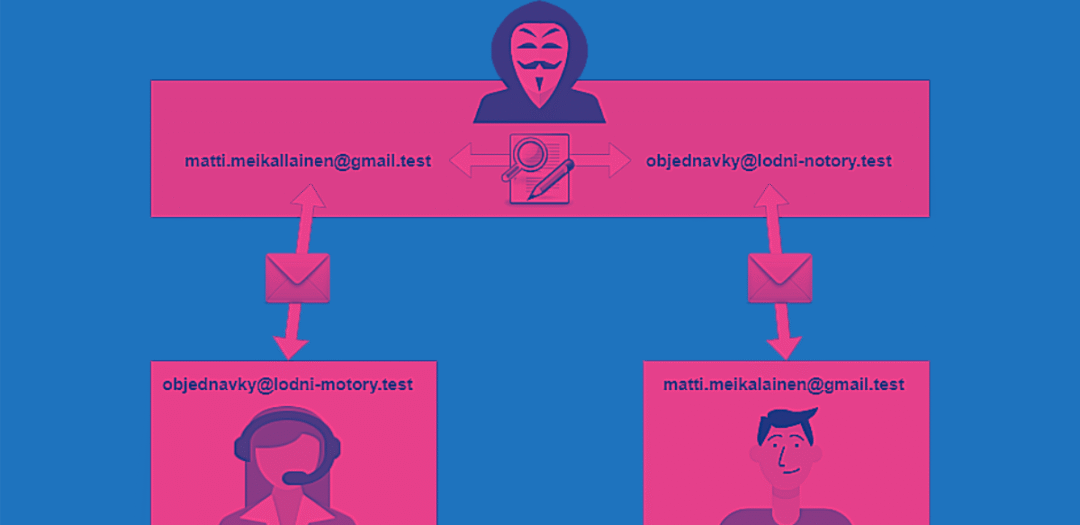
The criminals registered the e-mail that was similar to the victim’s email address matti.meikallainen@gmail.test. The address has double “L” in contrast to the victim’s actual e-mail address.
They have also registered the “lodni-notory.test“ domain. The letter M in the word motory has been replaced by N.
Their goal was for all communication between the victim and the producer to take place through them. So that they can manipulate the entire communication. We would call this “man in the middle“ attack.

Step #4: Realization Of Fraud
The fraud is getting finalized. The criminals started an e-mail communication that looked like this:
- The criminals sent the victim an e-mail claiming to be a manufacturer. They write that the engine they wanted to buy is in a special promo with a 20% discount, but only until stocks run out.
As this e-mail is a follow up to the previous communication, the victim did not notice that the sender’s address is “objednavky@lodni-notory.cz” and not “objednavky@lodni-motory.cz”. - As the victim wanted the engine, it took advantage of this “exceptional and significant” discount and placed the order.
- The criminals took the order, modified it a bit (omitted information about the discount), and forwarded it on behalf of the victim to the manufacturer.
- The manufacturer has accepted the order and issued a proforma invoice. It was then sent to the criminals (to a double L e-mail address).
- The criminals took the proforma invoice and modified the bank account number and the price. The invoice with a notification of a change in the bank account number was then forwarded to the victim.
- The invoice, except for the account number, looked completely legitimate (because it was the “original” invoice). As the e-mails contained contact details, the invoice looked as it always did (the victim had already done business with the manufacturer) and the communication followed up on earlier emails, the victim paid the invoice. The criminals received the money and the fraud was completed.
Interesting Features Of These Scams
It may not seem at first glance, but these scams are pretty tricky. Classic defense technologies are unable to deter them. Not a sandbox nor an antivirus would work because it is not a virus. Antispam is also not used because fraudsters own the domain and can have the SPF and DKIM set up correctly.
Users may not even notice “illegitimate” email addresses because many email clients only display the sender’s name (text specified by the sender). As communication refers to an earlier communication, the user usually does not suspect that the sender may be someone “else” (a fraudster).

As with ransomware attacks, this is the case of organized crime. However, these criminal groups are different. Somewhat different “skills” are required. Deep technical knowledge is the most important thing for ransomware attacks. The most important skill with BEC frauds is “social engineering” – the ability to deceive and manipulate people.
What To Do If a Fraud is Concluded
It is important to contact a bank and try to return the transfer as soon as possible. Fraudsters are aware that victims will try to save money. Therefore, they try to “move” the money as soon as they receive it (next time in detail) so that the payment cannot be returned. The later the victim discovers the fraud, the worse.
Furthermore, you need to remember that fraudsters “milk” their victims until they are discovered. Such as is the case with the Norfund story. Therefore, every incident needs to be investigated thoroughly. It should be investigated where could the information leak, and whether a company email is still under their control.
How To Avoid Getting Scammed
I know that we, as an IT company, are not able to fully defend against these scams (or I can’t think of how).
However, we can at least do something about it. As an IT provider, we should ensure that fraudsters are not able to access any corporate e-mail inbox, which they could use to “extract” information and send e-mails. It is ideal to use multifactor authentication also for e-mails and to monitor where users access the e-mail box from (IP addresses and their geographical affiliation). We can also check the rules for sorting mail (such as no mail forwarding outside the company is performed).
All changes to bank accounts or contact details should also be verified via another “communication medium”. Such as in case the supplier sends information about the account change via e-mail, it should be also verified by phone. It is important to use a number known in advance and not the one listed in the e-mail. It is rather easy for fraudsters to change the number in the signature for their own. The more money is the fraud aimed at, the more sophisticated the scammers will be.
The urgency to make the payment or request for confirmation of transfer can be yet another warning signal (Scammers want to request these to launder the money through “money mules”). Therefore, it may be good to set some rules within the company (eg payment requests are always processed after 24 hours) with no exceptions unless approved in person (fraudsters like to steal the identity of executives or business owners and utilizing this “authority” urge responsible staff to make the payment).
Conclusion
The article is just a quick summary of the “Business E-mail Compromise” topic It’s sort of topic “kick-off”. I would love to know, whether this topic interests you and whether you have encountered these scams recently.
For those curious, I recommend the lecture “Business Email Compromise: Operation Wire Wire and New Attack Vectors“.
Have a good time.
Good luck and safe networks.
Martin












Discussion