Password Management 2: We Have Installed Remote Desktop Manager
When I published an article about password management a month ago, I did not know how fast things would change. Around this time, we’ve been upgrading the Thycotic Secret Server to a higher edition (due to functionality). But the price offer has taken my breath away. When we bought it in 2012, we got 5 licenses with annual support at about 4,300 CZK (the prices were still public). Gradually, it was getting more and more expensive, new editions were being created … until we have reached about 39 times the original price in 2018 (after 7 years). It is really too much! Moreover, this is not the only SW that we have to pay for.
It has slightly reminded me of the LogMeIn situation, which we have used before we have switched to TeamViewer. They have doubled the price in a year. They have introduced a new highest tariff and doubled the price again. The transition to a higher tariff got four times more expensive. So we have switched to TeamViewer.
Back to the story. We have requested a special price via Thycotic distributor due to upgrade. It seems unfair to pay everything as a new customer to me (ie regardless of existing licenses and support subscription). While we were waiting for the new offer, I was looking for alternatives and I came across Devolutions Remote Desktop Manager (RDM).
Remote Desktop Manager – what does it do?
RDM is used to manage passwords, just like the Thycotic Secret Server. In addition, it can manage “remote connections“(somehow I can not come up with a better name) and link them with the login information. That means that you save login information to a single software (user name, password, private keys, OTP) and define a remote connection (server address, port, and connection type as RDP, SSH, web, iLo). When you want to connect to the server/device, just double-tap. The RDM connection will create itself and automatically log you in. This saves us a tremendous amount of time!
We have used a shared Dropbox folder with remote connections configuration till this time (URL links, RDP configuration files, SSH lines, microtik address book) and the passwords were stored in the Secret Server. When someone wanted to connect, found a remote connection configuration in Dropbox, searched for the correct password in the Secret Server, and manually logged in. It came to me as normal. But since I met RDM, I wouldn´t go back. 🙂
Other features I like about RDM
(it can do so much more):
- Login data can be both a custom username and password, as well as private keys (such as SSH) and OTP passwords. Especially OTP (one time password) is an interesting feature. RDM can count one-time passwords, just as they do “authenticators” in their mobile. You only enter the initial secret into RDM (it can be read from QR codes when 2FA is turned on) and the calculation algorithm and RDM will calculate the OTPs themselves. As a result, you/your RDM team will also log in to services that require 2FA (two-factor authentication), and you do not have to worry about sharing OTP on your mobile. Of course, it is necessary to look at this feature even though it is “breaking down” a sense and security of 2FA a bit.
- Auto VPN dialing. If you need to dial a VPN for a connection to a customer, RDM will do it for you. When you finish the job, RDM VPN closes itself. All VPN configurations are stored in RDM and it supports most types/manufacturers. So you do not need to configure VPN on each admin of your PC separately. RDM also addresses the problem of NB users. For example, when you are in a corporate network, it recognizes it and does not dial VPN.
- The RDM user interface is very configurable. New sessions (remote connections) can be created into bookmarks (you can quickly orientate and switch between a large number of connections) or external windows that you can predict (eg RDP connection to server X you want to have open at all times on the middle monitor, while Y on the monitor on the right). I personally like bookmarks. We often work on multiple servers at the same time, and in this way, we can switch between the connections faster (it was to minimize the RDP, switch to another and maximize it before).
- We were pushed out of the server by a colleague occasionally (where only 1 connection was allowed) because we did not know that someone else was working on the server. RDM solves this problem. Once someone is logged in, the connection icon will change and the records will show who is using the connection. At the same time, it is possible to use the “check-in/out” connection „locking“ feature – then the connection is only available to the person who has locked it.
- Access control auditing works even better than with the Secret Server. With Secret Service, we knew WHEN and WHO has used/displayed the password. But we did not know HOW LONG was the person connected. Since the remote connection in the RDM itself, we also have the exact time FROM TILL WHEN and WHO and WHERE was logged in.
- Just like the Secret Server, RDM can also open a remote connection (RDP, SSH, Web) to the user without accessing/showing the password. Such is a good form of security.
- If you are doing repetitive action on remote servers/devices, macros will come in handy. It is possible to write repetitive actions and let them run automatically when connecting/disconnecting or requesting (eg automatic backup configuration of switch/router when disconnecting).
- RDM has a password generator as well as the Secret Server. I like the fact that RDM can generate pronounceable passwords that are useful if you ever need to remember them or to dictate them.
What do we expect from the Remote Desktop Manager?
I thought we might not find a technology that would leapfrog our efficiency just a few months ago. I thought we would rather move forward with little steps. RDM is a small revolution for us. Previously, the connection took somewhere between 20-30 seconds. Now it is about 5 seconds. Of course, if you have to work on a server for a few hours, it’s a negligible delay. But when you need to make a small adjustment (a few minutes of work) on 8 servers/devices, then it’s really noticeable.
It is extraordinary that the RDM allows us to raise the level of security without, and at the same time, does not negatively impacting our efficiency (see the previous paragraph). I have been working on a concept of improving our and our customers’ networks security for a few months. I’m very much attracted by the “tier” model (see Securing Privileged Access Reference Material) and “secured management stations” (see Privileged Access Workstations). I have expanded and adapted both to our environment, and now we are implementing it in practice (see Network Security: Tier model and PAW).
Before the RDM, I have had to address the question of how to handle a significant number of user accounts and be able to orient in them. E.g. someone accidentally misplacing the wrong login data on the wrong PC and have thus compromised the data. RDM handles this situation gracefully. The number of errors in the input is equal to 0. The fact that each server has its own login does not slow anybody down (one does not have to look for what belongs where, because RDM cares about linking session and login information). Additionally, we can automatically reach multiple devices using automatic VPNs without needing to “jump servers” on a target network.
RDM also has a free version that we use to work with customers who have their own IT administrator or a team. Thanks to this we can set the same security measures as we do for them (each server/device has its own login) while making it easier for them to work. Where the free version is not enough, we’ll get a paid one (about 3,000 CZK a license).
Comparison: RDM vs Thycotic Secret Server
RDM is a way forward compared to Secret Server, mainly because of the “remote connections” management that the Secret Server doesn´t have. I also like higher RDM security with a database server. Thanks to the second layer of encryption (“data source protection” feature), data stored for the database server is incomprehensible, and a password or a private key is required for decryption, but it never occurs on the database server. In addition, RDM is at a much better price than the Secret Server.
The Secret Server, on the other hand, is more powerful to work with passwords. It allows you to define your own types of “secrets” – the structures that are stored in the database (for example, you want to store your username, password and domain name for an AD account, but you want to save your username, password and site address). Secret Server can change passwords by itself (RDM can´t) depending on time or action of the user (eg weekly or when logging out of RDM).
I think that even the remote connection provisioning function without the user seeing the password will be safer with Secret Server than the RDM. I think that the passwords in RDM are passed in some form of inter-process communication (ie the user’s password will appear on the user’s PC). While the Secret Server is running “proxying” (connection) through a server with Secret Service installed (the password will NOT appear on a user PC
Conclusion
There has been a little over a month between the discovery of RDM and its full deployment in our company (installation and testing in virtual environments, testing in a production environment, company training, and manual migration of all data). Until then, we have enjoyed the product and believe in it. At the same time, I am glad that we are still able to quickly adapt and deploy new technologies (it is especially needed in IT, which is constantly changing).
Because this article is very “pro-RDM”. I would just like to share that we are not its distributors and nor have I been paid for the article in any way. 🙂 I’m just excited about its functionality and the benefits of our work.
By the way, since we have discovered RDM, I’ve already met 2 companies that also use it. So, the password management in Czechia will not be as bad as I have thought when writing the “Password Management” article.
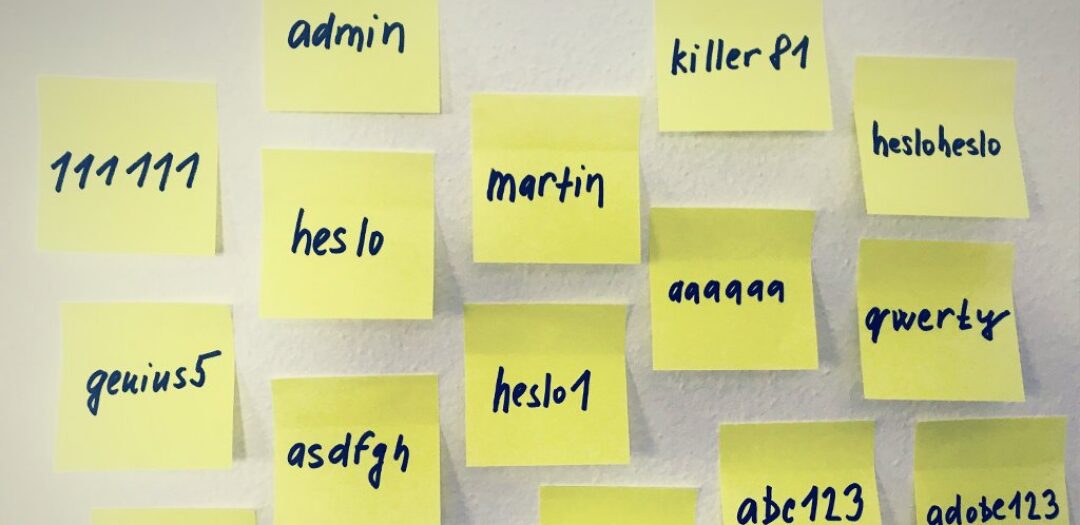
Have a nice day. And let your passwords never be broken. 😀












Discussion