Password Management
Today’s article will be a bit shorter, but more important. I would like to share with you how we handle customers´ passwords. It’s a very important thing because every IT company owns “keys” from all the data and systems of all its customers. If it is not done conscientiously, it can damage or destroy its customers (data loss, system shutdown, private information leak). I think that every customer should ask their IT administrator how they guard/handle the passwords for their systems.
On a lighter note, I will first describe what I have experienced.
What I have experienced
Using the same password for everything
We once got a customer for management who did not get any passwords from his former IT administrator. It’s not as taking over IT management couldn´t be done without passwords, it just slows the process down. Some systems need to “hacked” and some devices restarted to their factory settings. Then trying to re-configure the settings. In this case, however, I have managed to read the configuration of the switch through SNMP and get the password for its administration. Coincidentally, it was a universal password that has unlocked everything – even a domain administrator account!
Similar is the case with another customer, where the administrator has set up a domain administrator account in the multifunction printer. Most likely so the printer could scan through SMB to all folders on the server. Of course, it was not a problem to get the password from the printer. Especially if the default administration printer password is not changed. 😀
The administrator in either case probably didn´t know that the password could be extracted from the device. But you can not rely on it. Better think that all passwords can be extracted. At the same time, it is unthinkable to use a universal password for all accounts. It may stop a computer virus, but not a human attacker. Such companies work only due to the fact no one has ever attempted to hack them.
Using one password for multiple customers
Last year, we have undertaken to service a company that was unhappy with its former external IT administrator. Everything was done in a friendly spirit. We have received a new domain administrator account. They gave us passwords to all other devices. At the time of the audit, I have encountered a saved password for their company user account on a server. I have pulled the password from curiosity (to know how complex passwords they use). Since I was very curious, I have tried to make sure that this password would not work for other customers of this IT company as well. You wouldn´t believe me what I came to. The company used the same password for domain administrators across its customers. I do think there is no need to comment any further.
Btw. we still have this password today and is still valid. So if you know someone along these lines, you’d better change your passwords. 😀
I suspect that there are many more such “offenders”. It has happened also happened that some company was not able to provide us with a management password immediately, but only after a few days. Is that because they had to change the password before they would share it?
I think that businesses do so because they do not have any password management tool. But they want to share passwords with each other in some way. So there are just 4 main passwords that are used everywhere. However, it is dangerous for the customer. The password could leak somewhere – for example, it is input on a compromised computer, someone watches over the shoulder or saves it somewhere by an error. At the same time, I do not know how they would deal with the situation when someone who knows the password leaves the company. It does not seem real to me to change the password in hundreds of places (especially when you do not even know where it is used).
Password management in Excel and password managers
I have already met with numerous IT outsourcing companies and internal IT departments that share/manage passwords in Excel. In fact, I thought it was a strange thing at first because Excel was not designed for such purposes. However, I was looking at the power of Excel file encryption, and it is acceptable from Excel 2007 (XLSX format) onwards, so I have nothing to say in this regard – of course, if you use a strong password. However, I find the disadvantage in no audit of access to passwords. The file (so all passwords) can be easily copied and permissions can´t be controlled.
In addition, I can imagine password management in a password manager (ideal for individuals). Applications are designed for password management, and the level of database encryption is set accordingly. Alternatively, there may be some online password manager (passwords are in the cloud and you have access to them). I think these are good variants. Keep in mind, however, that does not mean you are absolutely safe.
For example, if you have a password manager opened, the master password (password to open password database) can be read through a different application (eg https://github.com/HarmJ0y/KeeThief). In combination with Bash Bunny, I will get the password and the database itself in 20 seconds. 😀 We´ve already experienced one hacked online password manager – OneLogin. And the mobile password management applications did not do so well either – 9 Popular Password Manager Apps Found Leaking Your Secrets. Extra care is needed.
How do we manage passwords
I have always taken the password management seriously. I would find it unprofessional to use weak and non-unique passwords. Therefore, we use unique and complex (random) passwords for all customers that are different for each account, device, or website. At present, we have over 2,500 unique passwords in our database. To do this we use a tool, of course.
I will allow myself another small turn here. For attacker/penetration tester, there is nothing more beautiful than “recycling” passwords = using the same/template password in multiple places. In recent years, there have been a large number of login leaks from known services (MySpace, Adobe, Badoo, Mall.com, Dropbox, LinkedIn, Last.Fm, Badoo, Tumblr, etc.). Once we know someone’s e-mail address, we will try to search the password in the escaped databases. We test this password against other services and believe me, it works – it takes only a few tens of minutes.
You can easily check whether your login details are freely available on the internet at: Have I Been Pwned?
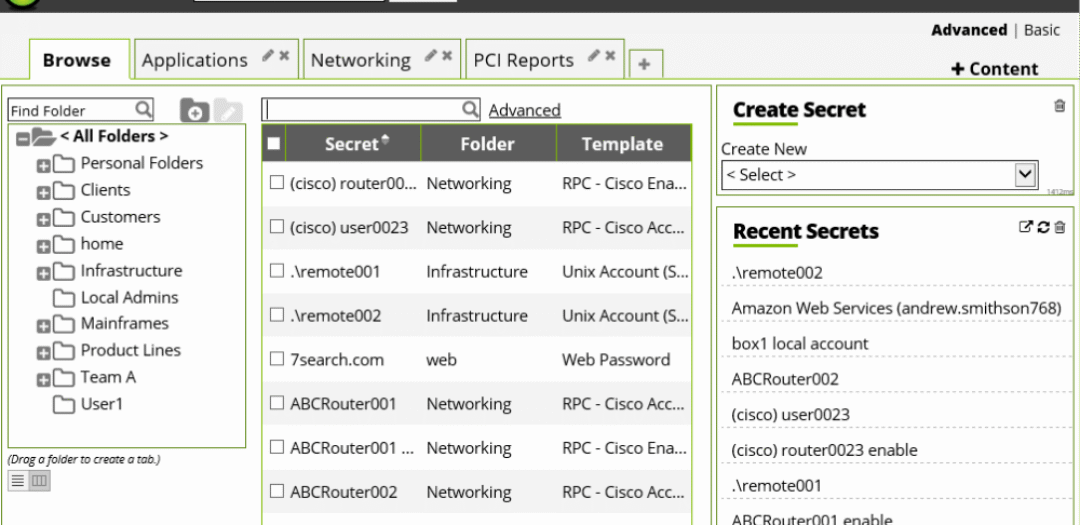
We use Secret Server from Thycotic ever since the PATRON-IT has been established. This is a web-based password management application hosted on our own server (I do not want to share such sensitive data to the cloud).
The benefits of working with Secret Server:
- Everyone has their login information in the Secret Server.
- We audit who is accessing which passwords (Thycotic also has a Privileged Behavior Analytics add-on, which we do not have yet).
- Everyone can only access the passwords they need for their work.
- It is not possible to copy the entire database in common ways.
- Allows the user to connect to the RDP or SSH server without displaying the password (it has Proxy Modules). In the case of Proxy Modules, it can record RDP session video and SSH session (but recording also requires an addon).
- I can change passwords to a variety of services myself (Windows, Active Directory, LDAP, SSH, telnet …). This is suitable, for example, for a regular change of passwords (eg 1/month) or when needed (for example when an employee leaves).
Conclusion
If you like the Secret Server, try a free version Secret Server Free. It is limited by the functionality and the number of saved passwords. The paid version is relatively expensive. 🙁 Thycotic has switched to affiliate sales a few years ago (formerly distributed directly) and the price has increased several times.
If you would make use of a documentation system, have a look at ITGlue. They have a documentation system that includes password management. I was also considering it for a while.
How do you handle password management? Do you also have some “funny” stories?
EDIT 19.3.2018: We have installed a new password management systém, please have a look at what it can do: Password Management 2: We Have Installed Remote Desktop Manager.











Discussion